John the Ripper (also called simply ‘John’ ) is the most well known free password cracking tool that owes its success to its user-friendly command-line interface. John has autodetect capability. Hello FriendsIn this video I will talk about How to Crack Encrypted Hash Password - Using John The Ripper.-. Either add functionality to John the Ripper to support sheet protection passwords (which you'll need to keep separate from the existing Office encryption functionality), or write your own cracker based on the algorithm. How to crack SHA512 hexdigest passwords with John the Ripper?
John the Ripper is a favourite password cracking tool of many pentesters. There is plenty of documentation about its command line options.
I’ve encountered the following problems using John the Ripper. These are not problems with the tool itself, but inherent problems with pentesting and password cracking in general.
- Sometimes I stumble across hashes on a pentest, but don’t recognise the format, don’t know if it’s supported by john, or whether there are multiple “–format” options I should try.
- The hashes you collect on a pentest sometimes need munging into a different format… but what’s the format john is expecting?
- John will occasionally recognise your hashes as the wrong type (e.g. “Raw MD5″ as “LM DES”). This is inevitable because some hashes look identical.
- Sometimes I gain access to a system, but can’t recall how to recover the password hashes for that particular application / OS.
These problems can all be sorted with a bit of googling or grepping through the john source code. I thought it might be helpful to compile a cheat sheet to reduce the amount of time I spend grepping and googling.
In the first release of this page I’ve:
- Copied example hashes out of the source code for most supported hash types.
- Provided examples of what your hashes.txt file might look like (though I’m sure other variations are supported that aren’t covered here yet).
- For each example hash I’ve stated whether it will be automatically recognised by john, or whether you’ll have to use the “–format” option (in which case I’ve included which –format option you need)
I haven’t yet done the following:
- Added reminders on how hashes can be collected.
- Added information on how to munge the hashes into a format supported by john.
This sheet was originally based on john-1.7.8-jumbo-5. Changes in supported hashes or hash formats since then may not be reflected on this page.
afs – Kerberos AFS DES
Supported Hash Formats
bfegg – Eggdrop
Supported Hash Formats
bf – OpenBSD Blowfish
Supported Hash Formats
bsdi – BSDI DES
Supported Hash Formats
crypt – generic crypt(3)
Supported Hash Formats
des – Traditional DES
Supported Hash Formats
dmd5 – DIGEST-MD5
Supported Hash Formats
TODO: No working example yet.
dominosec – More Secure Internet Password
Supported Hash Formats
<none> – EPiServer SID Hashes
Supported Hash Formats
hdaa – HTTP Digest access authentication
Supported Hash Formats
hmac-md5 – HMAC MD5

Supported Hash Formats
hmailserver – hmailserver
Supported Hash Formats
ipb2 – IPB2 MD5
Supported Hash Formats
krb4 – Kerberos v4 TGT
Supported Hash Formats

krb5 – Kerberos v5 TGT
Supported Hash Formats
lm – LM DES
Supported Hash Formats
lotus5 – Lotus5
Supported Hash Formats
md4-gen – Generic salted MD4
Supported Hash Formats
md5 – FreeBSD MD5
Supported Hash Formats
md5-gen – Generic MD5
Supported Hash Formats
TODO: No working example yet.
mediawiki – MediaWiki MD5s
Supported Hash Formats
mscash – M$ Cache Hash
Supported Hash Formats
mscash2 – M$ Cache Hash 2 (DCC2)
Supported Hash Formats
mschapv2 – MSCHAPv2 C/R MD4 DES
Supported Hash Formats
mskrb5 – MS Kerberos 5 AS-REQ Pre-Auth
Supported Hash Formats
mssql05 – MS-SQL05
Supported Hash Formats
mssql – MS-SQL
Supported Hash Formats
mysql-fast – MYSQL_fast
Supported Hash Formats
mysql – MYSQL
Supported Hash Formats
mysql-sha1 – MySQL 4.1 double-SHA-1
Supported Hash Formats

netlm – LM C/R DES
Supported Hash Formats
netlmv2 – LMv2 C/R MD4 HMAC-MD5
Supported Hash Formats
netntlm – NTLMv1 C/R MD4 DES [ESS MD5]
Supported Hash Formats
netntlmv2 – NTLMv2 C/R MD4 HMAC-MD5
Supported Hash Formats
nethalflm – HalfLM C/R DES
Supported Hash Formats

md5ns – Netscreen MD5
Supported Hash Formats
nsldap – Netscape LDAP SHA
Supported Hash Formats
ssha – Netscape LDAP SSHA
Supported Hash Formats
nt – NT MD4
Supported Hash Formats
openssha – OpenLDAP SSHA
Supported Hash Formats
oracle11 – Oracle 11g
Supported Hash Formats
oracle – Oracle
Supported Hash Formats
pdf – pdf
Supported Hash Formats
phpass-md5 – PHPass MD5
Supported Hash Formats
phps – PHPS MD5
Supported Hash Formats
pix-md5 – PIX MD5
Supported Hash Formats
po – Post.Office MD5
Supported Hash Formats
rar – rar
Supported Hash Formats
raw-md4 – Raw MD4
Supported Hash Formats
raw-md5 – Raw MD5
Supported Hash Formats
raw-md5-unicode – Raw MD5 of Unicode plaintext
Supported Hash Formats
raw-sha1 – Raw SHA-1
Supported Hash Formats
raw-sha224 – Raw SHA-224
Supported Hash Formats
raw-sha256 – Raw SHA-256
Supported Hash Formats
raw-sha384 – Raw SHA-384
Supported Hash Formats
raw-sha512 – Raw SHA-512
Supported Hash Formats
salted-sha – Salted SHA
Supported Hash Formats
sapb – SAP BCODE
Supported Hash Formats
sapg – SAP CODVN G (PASSCODE)
Supported Hash Formats
sha1-gen – Generic salted SHA-1
Supported Hash Formats
skey – S/Key
Supported Hash Formats
TODO: No working example yet.
TODO: No working example yet.
TODO: No working example yet.
TODO: No working example yet.
ssh – ssh
Supported Hash Formats
sybasease – sybasease
Supported Hash Formats
xsha – Mac OS X 10.4+ salted SHA-1
Supported Hash Formats
zip – zip
Supported Hash Formats
Tags: johntheripper, pentest
Posted in Cheat Sheets
John The Ripper Crack Sha512 Encryption Key
Introduction
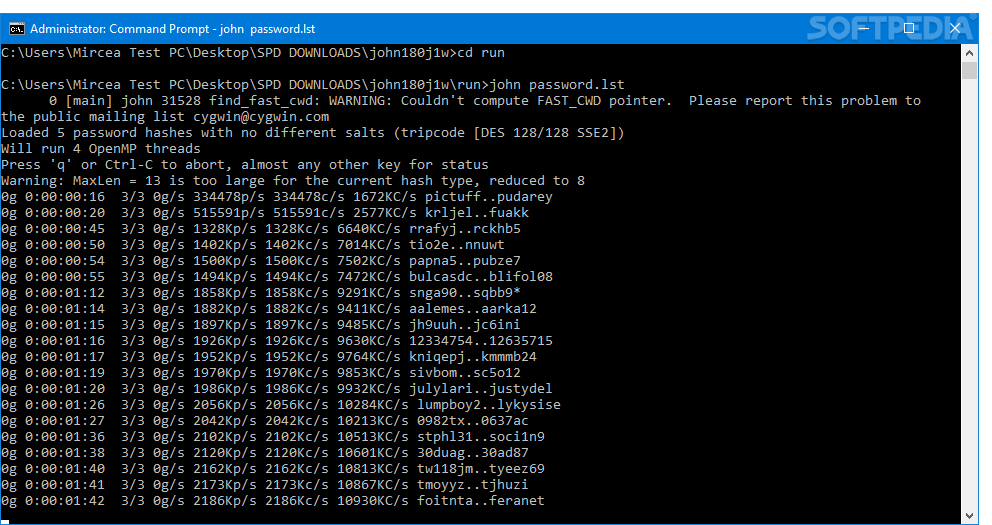
John the Ripper (JTR) is a widely known and verified fast password cracker, available for Windows, DOS, BeOS, and OpenVMS and many flavours of Linux. It uses wordlists/dictionary to crack many different types of hashes including MD5, SHA, etc.
John the Ripper: Fast Password Cracker
This password cracking tool is free and Open Source, initially developed for the Unix operating system. But today it runs on fifteen different platforms. Its primary purpose is to detect weak Unix passwords. Besides several crypt(3) password hash types most commonly found on various Unix systems, supported out of the box are Windows LM hashes, and a lot of other hashes and ciphers in the community-enhanced version.
For those who rather use commercial version, John the Ripper is available for following platforms:
- Linux: John the Ripper Pro
- Mac OS X: John the Ripper Pro
- Windows: Hash Suite
- Android: Hash Suite Droid
John the Ripper offers two types of attacks:
- Dictionary: It takes text string samples from wordlist, which contains dictionary of real passwords that are cracked before, encrypting it in the same format as the password being examined (encryption algorithm/key), and comparing the output to the encrypted string. John can also perform word alterations.
- Brute force: It goes through all the possible plaintexts, hashing each one and then comparing it to the input hash. This method takes a long time to run, but it’s precious for cracking password that doesn’t appear in wordlist dictionary.
Features/Performance
- Feature-rich and fast password cracking tool, with several cracking modes.
- It allows you to define a custom cracking mode using the built-in compiler supporting a subset of C.
- You can use same cracker everywhere, since John is available for different platforms, with possibility to continue a cracking session started on another platform.
- This tool supports a lot of Unix crypt(3) hash types:
traditional DES-based,'bigcrypt',BSDI extended DES-based,FreeBSD MD5-based,OpenBSD Blowfish-based,Kerberos/AFS and Windows LM (DES-based),DES-based tripcodes.
- On Linux distributions with
glibc 2.7+, John 1.7.6+ supportsSHA-crypthashes, with optional OpenMP parallelization (requires GCC 4.2+). - On recent versions of Solaris, John 1.7.6+ supports and autodetects
SHA-cryptandSunMD5hashes, also with optional OpenMP parallelization (requires GCC 4.2+ or recent Sun Studio). - John the Ripper Pro adds support for Windows NTLM (MD4-based) and Mac OS X 10.4+ salted SHA-1 hashes.
- “Community enhanced” -jumbo versions add support for many more password hash types:
- Windows NTLM (
MD4-based), Mac OS X 10.4-10.6salted SHA-1hashes, Mac OS X 10.7salted SHA-512hashes, rawMD5andSHA-1, arbitraryMD5-based“web application” password hash types, hashes used by SQL database servers (MySQL, MS SQL, Oracle) and by some LDAP servers, several hash types used on OpenVMS, password hashes of the Eggdrop IRC bot, and lots of other hash types, as well as many non-hashes such as OpenSSH private keys, S/Key skeykeys files, Kerberos TGTs, PDF files, ZIP (classic PKZIP and WinZip/AES) and RAR archives.
- Windows NTLM (
- John the Ripper has its own highly optimized modules for different hash types and processor architectures.
John the Ripper’s Cracking Modes:
- Wordlist mode
- Single crack mode
- Incremental mode
- External mode
Install
Debian-based systems/Ubuntu
Clone it from the Github repository:
Then build:
To test your build, run:
Windows
Windows users can find detailed documentation on the official John the Ripper Wiki page.
Usage
To run John, firstly supply it with some password files and if you wish, specify a cracking mode:
John The Ripper Crack Sha512 Encryption Decryption
If you want to restrict it to the wordlist mode only (permitting the use of word mangling rules):
To retrieve the cracked passwords, run:
Interrupted session can be continued with the following:
Sha512 Crypt
Options
